Your organization wants to advance its security-management capabilities and has already started moving some workloads to the public cloud.
You’re evaluating security information and event management (SIEM) solutions that can help in both an on-premises and a multiple-cloud environment. You’ve heard about Azure Sentinel and want to find out whether it could be the right SIEM solution for your business.
Ideally, you’d select a service that provides the features and functionality that you need, with minimal administration and a flexible pricing model.
Azure Sentinel offers exactly those benefits.
In this post, we will explore Azure Sentinel and discover why and when to use it.
What is security incident and event management (SIEM)?
A SIEM system is a tool that an organization uses to collect, analyze, and perform security operations on its computer systems. Those systems can be hardware appliances, applications, or both.
In its simplest form, a SIEM system enables you to:
- Collect and query logs.
- Do some form of correlation or anomaly detection.
- Create alerts and incidents based on your findings.
A SIEM system might offer functionality such as:
- Log management: The ability to collect, store, and query the log data from resources within your environment.
- Alerting: A proactive look inside the log data for potential security incidents and anomalies.
- Visualization: Graphs and dashboards that provide visual insights into your log data.
- Incident management: The ability to create, update, assign, and investigate incidents that have been identified.
- Querying data: A rich query language, similar to that for log management, that you can use to query and understand your data.
What is Azure Sentinel?
Azure Sentinel is a cloud-native SIEM system that a security operations team can use to:
- Get security insights across the enterprise by collecting data from virtually any source.
- Detect and investigate threats quickly by using built-in machine learning and Microsoft threat intelligence.
- Automate threat responses by using playbooks and by integrating Azure Logic Apps.
Unlike with traditional SIEM solutions, to run Azure Sentinel, you don’t need to install any servers either on-premises or in the cloud. Azure Sentinel is a service that you deploy in Azure. You can get up and running with Sentinel in just a few minutes in the Azure portal.
Azure Sentinel is tightly integrated with other cloud services. Not only can you quickly ingest logs, but you can also use other cloud services natively (for example, authorization and automation).
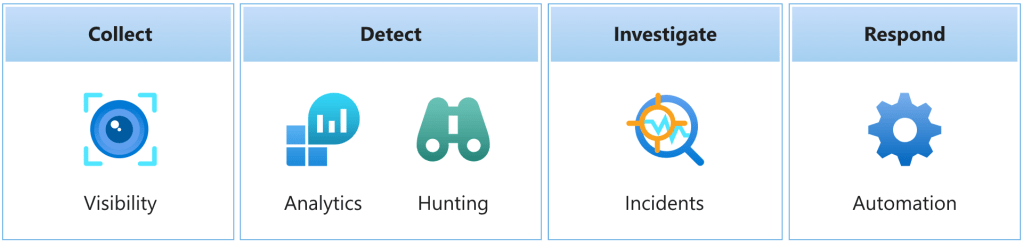
Azure Sentinel helps you enable end-to-end security operations including collection, detection, investigation, and response:
How Azure Sentinel works
Azure Sentinel helps you enable end-to-end security operations. It starts with log ingestion and continues through to automated response to security alerts.
Here are the key features and components of Azure Sentinel.
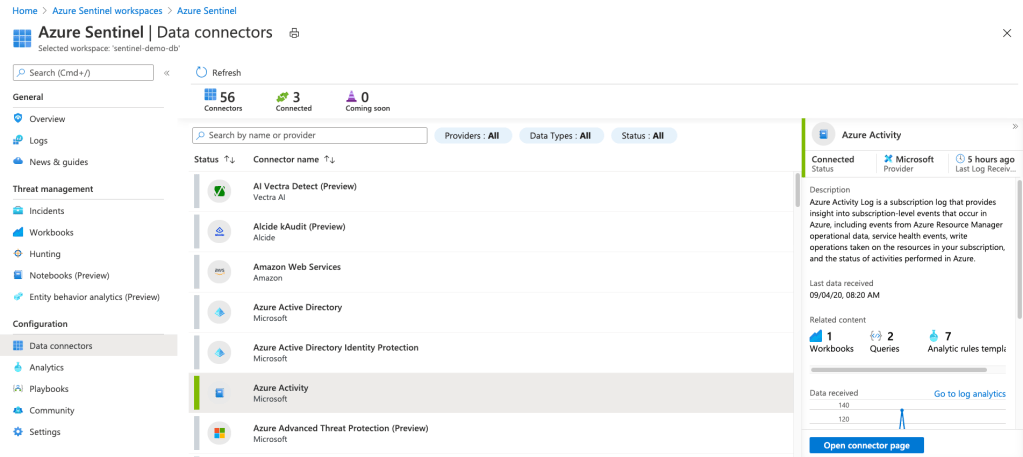
Data connectors
The first thing to do is to have your data ingested into Azure Sentinel. Data connectors enable you to do just that. You can add some services, such as Azure activity logs, just by selecting a button. Others, such as syslog, require a little configuration. There are data connectors that cover all scenarios and sources, including but not limited to:
- syslog
- Common Event Format (CEF)
- Trusted Automated eXchange of Indicator Information (TAXII) (for threat intelligence)
- Azure
- AWS services
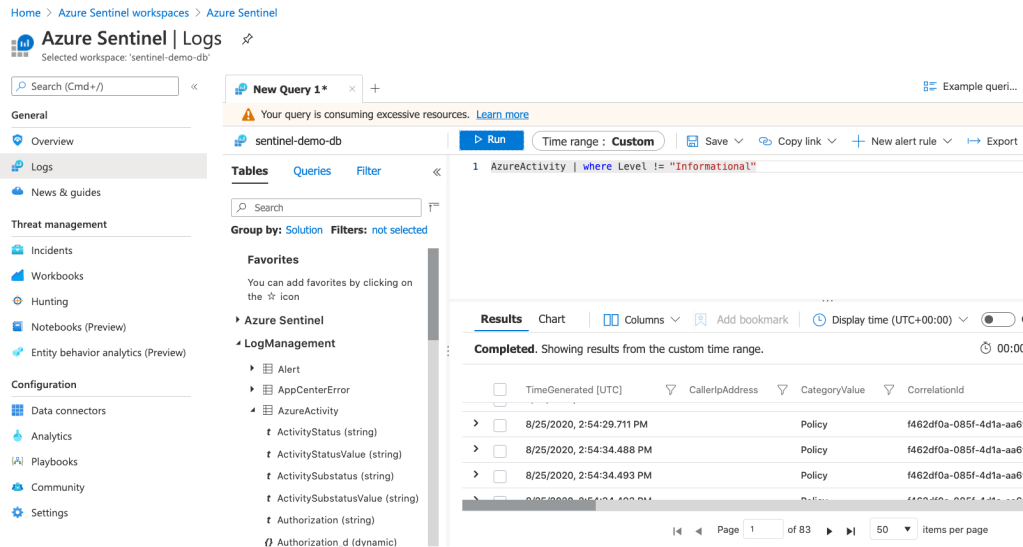
Log retention
After it’s been ingested into Azure Sentinel, your data is stored by using Log Analytics. The benefits of using Log Analytics include the ability to use the Kusto Query Language (KQL) to query your data. KQL is a rich query language that gives you the power to dive into and gain insights from our data.
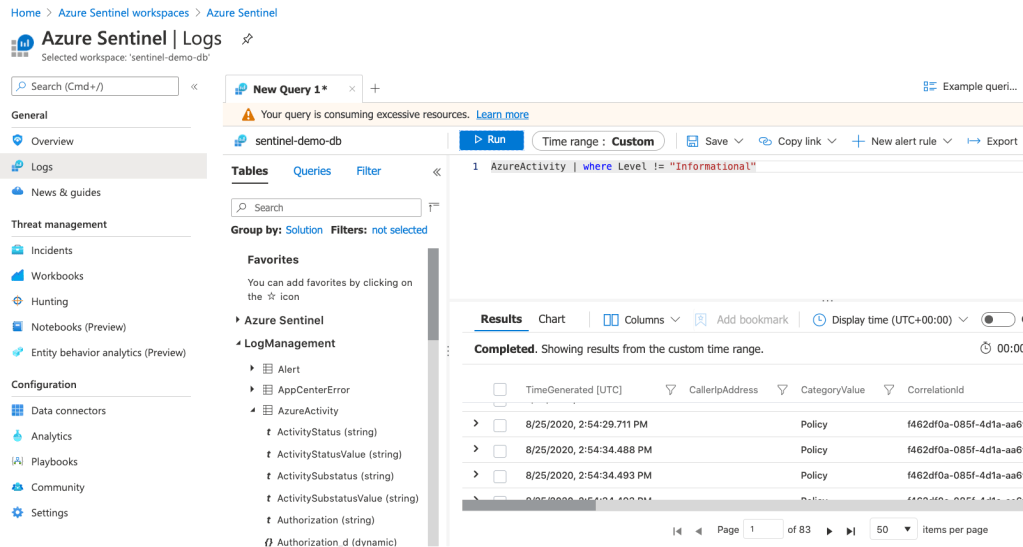
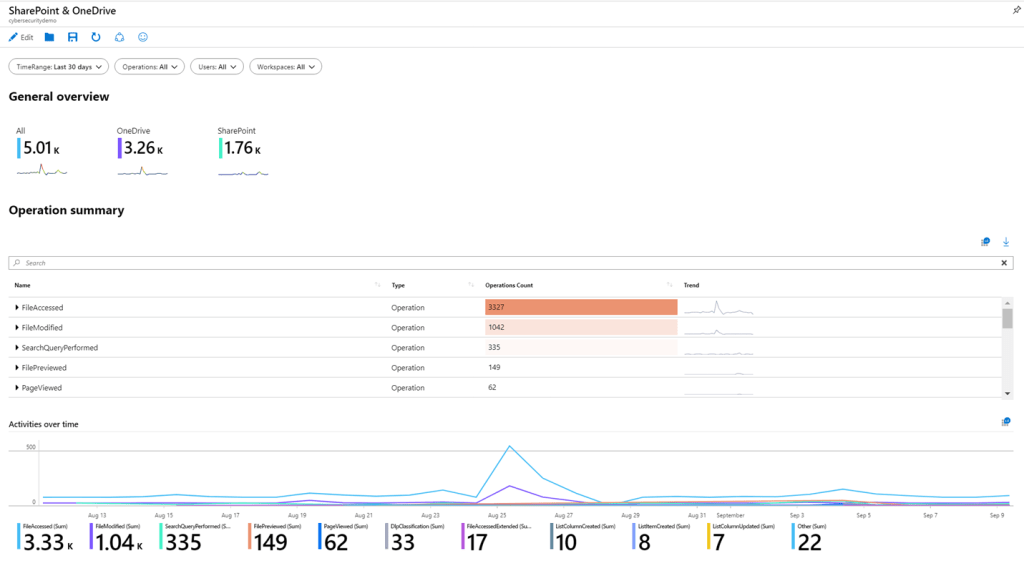
Workbooks
You use workbooks to visualize your data within Azure Sentinel. Think of workbooks as dashboards. Each component in the dashboard is built by using an underlying KQL query of your data. You can use the built-in workbooks within Azure Sentinel, edit them to meet your own needs, or create your own workbooks from scratch.
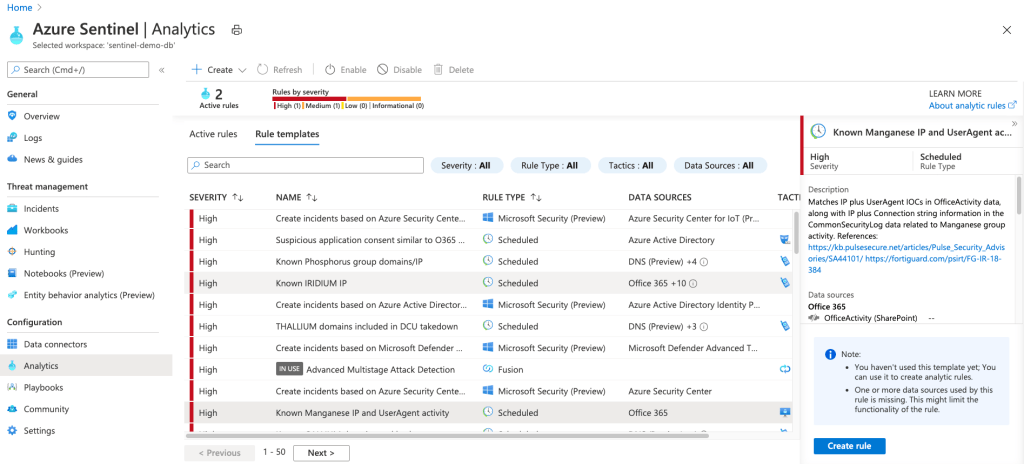
Analytics Alerts
So far, you have your logs and some data visualization. Now it would be great to have some proactive analytics across your data, so you’re notified when something suspicious occurs. You can enable built-in analytics alerts within your Sentinel workspace. There are various types of alerts, some of which you can edit to your own needs. Other alerts are built on machine-learning models that are proprietary to Microsoft. You can also create custom, scheduled alerts from scratch.
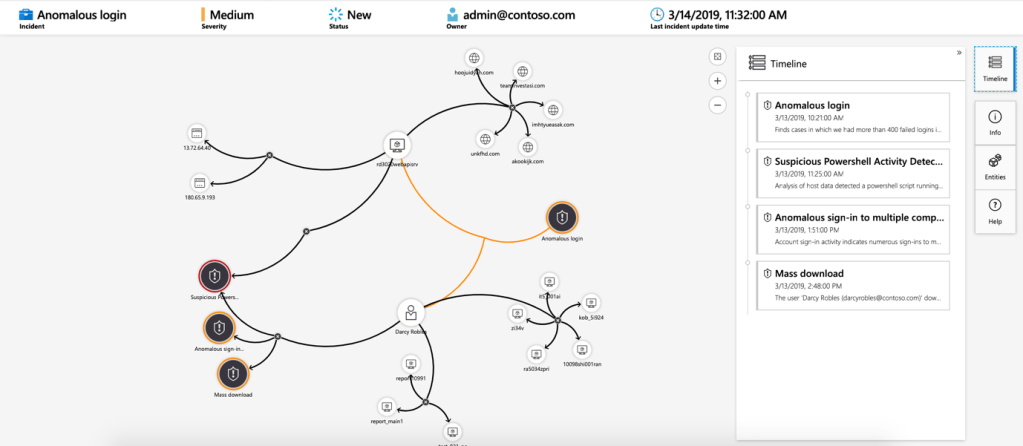
Incidents and investigations
An incident is created when an alert that you’ve enabled is triggered. In Azure Sentinel, you can do standard incident management tasks like changing status or assigning incidents to individuals for investigation. Azure Sentinel also has investigation functionality, so you can visually investigate incidents by mapping entities across log data along a timeline.
Automation playbooks
With the ability to respond to incidents automatically, you can automate some of your security operations and make your SOC more productive. Azure Sentinel integrates with Azure Logic Apps, enabling you to create automated workflows, or playbooks, in response to events. This functionality could be used for incident management, enrichment, investigation, or remediation. These capabilities are often referred to a security orchestration, automation, and response (SOAR).
You now start to see how Azure Sentinel might help you achieve your goals. For example, you could:
- Ingest data from you cloud and on-premises environments.
- Perform analytics on that data.
- Manage and investigate any incidents that occur.
- Perhaps even respond automatically by using playbooks.
Azure Sentinel gives you an end-to-end solution for you security and compliance needs.
Contact Remedia Security if you are interested in learning more about how Azure Sentinel can improve your cybersecurity and compliance program.



